Restricting Which LDAP Users Can Log In
Overview
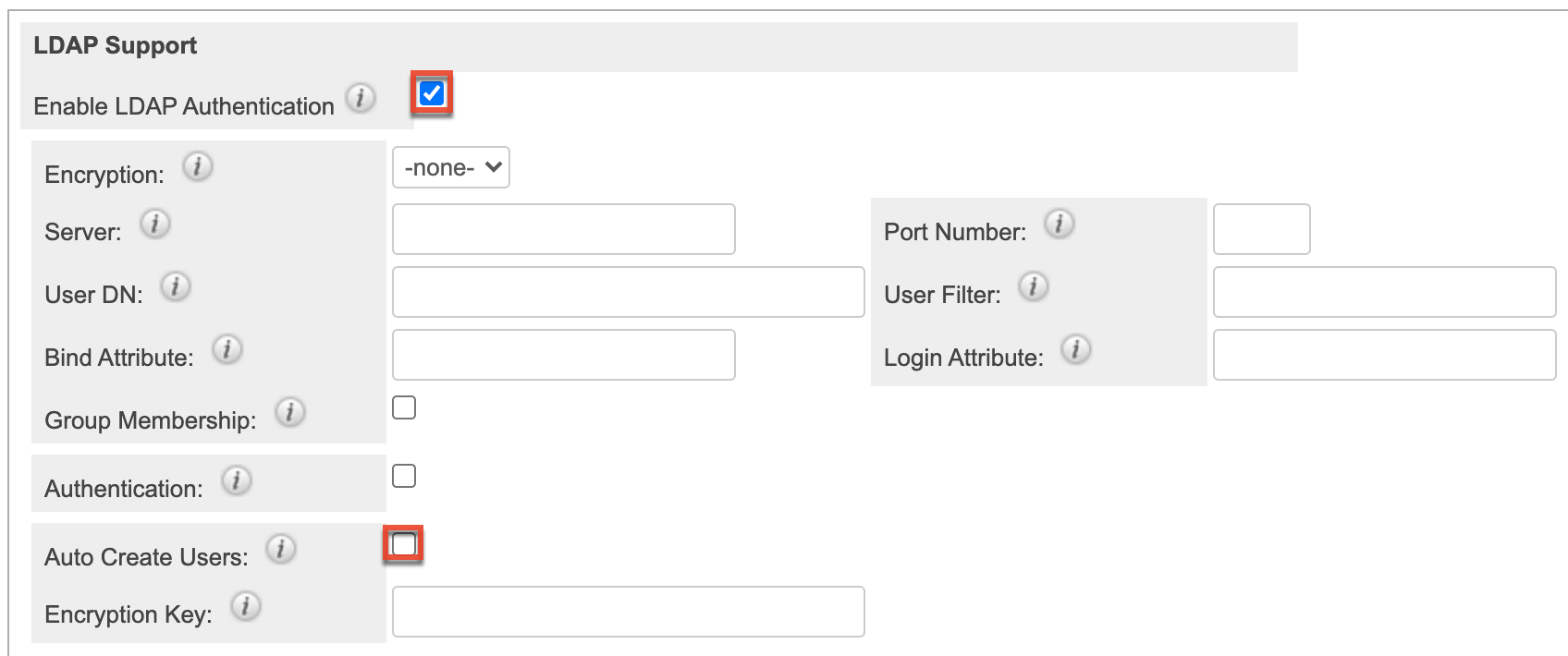
With LDAP configured with Sugar, you may have settings established that allow any user who enters their LDAP credentials to log in to Sugar. This creates a new user account for each individual that logs in and can inadvertently exceed your license count or grant unintended access to sensitive data. This article covers how to ensure that only users who are explicitly created in Sugar can log in with their LDAP credentials.
Note: For instances that use SugarIdentity, LDAP is configured in SugarIdentity. So, you will need to disable the Auto Create Users option (mentioned in the below section) in SugarIdentity instead.
Prerequisites
- You must be an administrator or have developer-level role access to make the necessary changes in Admin > Password Management.
- You must already have LDAP authentication enabled under Admin > Password Management > LDAP Support.
Steps to Complete
- Log in as an administrator and go to Admin > Password Management.
- Scroll down to the LDAP Support section.
- Ensure that the Auto Create Users option is disabled. If it is not, then disable the option by removing the checkmark from the box.
- Click "Save" to finalize your changes.
Application
Once this change has been saved, only users who were specifically created within your Sugar instance will be able to log in with their LDAP credentials. For more information on LDAP configuration in Admin > Password Management, refer to the Password Management documentation.